CompTIA CV0-004 Übungsprüfungen
Zuletzt aktualisiert am 24.03.2026- Prüfungscode: CV0-004
- Prüfungsname: CompTIA Cloud+ (2024)
- Zertifizierungsanbieter: CompTIA
- Zuletzt aktualisiert am: 24.03.2026
Which of the following is a difference between a SAN and a NAS?
- A . A SAN works only with fiber-based networks.
- B . A SAN works with any Ethernet-based network.
- C . A NAS uses a faster protocol than a SAN
- D . A NAS uses a slower protocol than a SAN.
An organization wants to ensure its data is protected in the event of a natural disaster. To support this effort, the company has rented a colocation space in another part of the country.
Which of the following disaster recovery practices can be used to best protect the data?
- A . On-site
- B . Replication
- C . Retention
- D . Off-site
A company recently migrated to a public cloud provider. The company’s computer incident response team needs to configure native cloud services tor detailed logging.
Which of the following should the team implement on each cloud service to support root cause analysis of past events? {Select two).
- A . Log retention
- B . Tracing
- C . Log aggregation
- D . Log rotation
- E . Hashing
- F . Encryption
An administrator is setting up a cloud backup solution that requires the following features:
• Cost effective
• Granular recovery
• Multilocation
Which of the following backup types best meets these requirements?
- A . Off-site, full, incremental, and differential
- B . Cloud site, full, and differential
- C . On-site. full, and incremental
- D . On-site. full, and differential
An administrator used a script that worked in the past to create and tag five virtual machines. All of the virtual machines have been created: however, the administrator sees the following results: { tags: [ ] }
Which of the following is the most likely reason for this result?
- A . API throttling
- B . Service quotas
- C . Command deprecation
- D . Compatibility issues
A cloud engineer is in charge of deploying a platform in an laaS public cloud. The application tracks the state using session cookies, and there are no affinity restrictions.
Which of the following will help the engineer reduce monthly expenses and allow the application to provide the service?
- A . Resource metering
- B . Reserved resources
- C . Dedicated host
- D . Pay-as-you-go model
A cloud engineer is reviewing a disaster recovery plan that includes the following requirements:
• System state, files, and configurations must be backed up on a weekly basis.
• The system state, file, and configuration backups must be tested annually.
Which of the following backup methods should the engineer implement for the first week the plan is executed?
- A . Differential
- B . Incremental
- C . Snapshot
- D . Full
A cloud networking engineer is troubleshooting the corporate office’s network configuration. Employees in the IT and operations departments are unable to resolve IP addresses on all devices, and the IT department cannot establish a connection to other departments‘ subnets.
The engineer identifies the following configuration currently in place to support the office network:
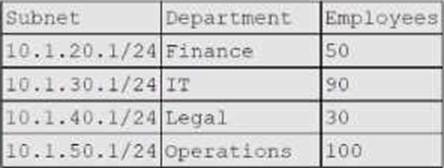
Each employee needs to connect to the network with a maximum of three hosts. Each subnet must be segregated, but the IT department must have the ability to communicate with all subnets.
Which of the following meet the IP addressing and routing requirements? (Select two).
- A . Modifying the subnet mask to 255 255 254.0 for IT and operations departments
- B . Configuring static routing to allow access from each subnet to 10.1.40.1
- C . Modifying the BYOD policy to reduce the volume of devices that are allowed to connect to the corporate network
- D . Configuring static routing to allow access from 10.1.30.1 to each subnet
- E . Combining the subnets and increasing the allocation of IP addresses available to support three hosts for each employee
- F . Modifying the subnet mask to 255.255.255.128 for the IT and operations departments
Given the following command:
Sdocker pull images.comptia.org/user1/myimage:latest
Which of the following correctly identifies images.comptia.org?
- A . Image registry
- B . Image creator
- C . Image version
- D . Image name
Which of the following vulnerability management concepts is best defined as the process of discovering vulnerabilities?
- A . Scanning
- B . Assessment
- C . Remediation
- D . Identification
