CompTIA CV0-004 Übungsprüfungen
Zuletzt aktualisiert am 24.03.2026- Prüfungscode: CV0-004
- Prüfungsname: CompTIA Cloud+ (2024)
- Zertifizierungsanbieter: CompTIA
- Zuletzt aktualisiert am: 24.03.2026
A company that has several branches worldwide needs to facilitate full access to a specific cloud resource to a branch in Spain. Other branches will have only read access.
Which of the following is the best way to grant access to the branch in Spain?
- A . Set up MFA for the users working at the branch.
- B . Create a network security group with required permissions for users in Spain.
- C . Apply a rule on the WAF to allow only users in Spain access to the resource.
- D . Implement an IPS/IDS to detect unauthorized users.
A cloud engineer is running a latency-sensitive workload that must be resilient and highly available across multiple regions.
Which of the following concepts best addresses these requirements?
- A . Cloning
- B . Clustering
- C . Hardware passthrough
- D . Stand-alone container
Department supervisors have requested a report that will help them understand the utilization of cloud resources, make decisions about budgeting for the following year, and reduce costs.
Which of the following are the most important requisite steps to create the report? (Select two).
- A . Set the desired retention of resource logs.
- B . Configure application tracing.
- C . Integrate email alerts with ticketing software.
- D . Enable resource tagging.
- E . Configure the collection of performance/utilization logs.
- F . Configure metric threshold alerts.
Five thousand employees always access the company’s public cloud-hosted web application on a daily basis during the same time frame. Some users have been reporting performance issues while attempting to connect to the web application Which of the following is the best configuration approach to resolve this issue?
- A . Scale vertically based on a trend.
- B . Scale horizontally based on a schedule
- C . Scale vertically based on a load.
- D . Scale horizontally based on an event
Which of the following Al/ML technologies consumes text input to discern tone?
- A . Text recognition
- B . Computer vision
- C . Visual recognition
- D . Sentiment analysis
A cloud administrator wants to provision a host with two VMs.
The VMs require the following:
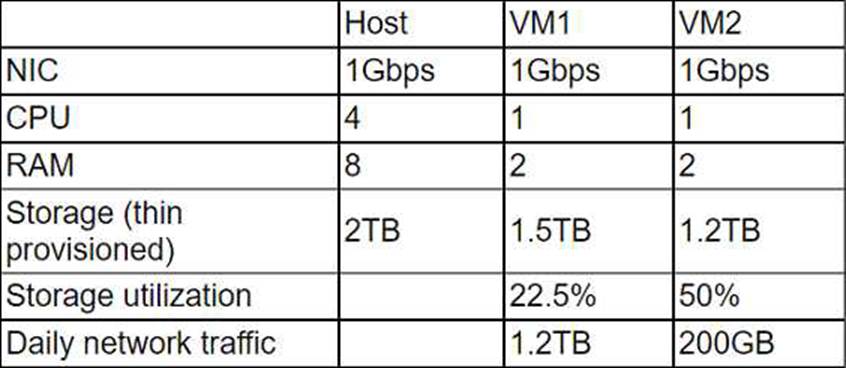
After configuring the servers, the administrator notices that during certain hours of the day, the performance heavily degrades.
Which of the following is the best explanation?
- A . The host requires additional physical CPUs.
- B . A higher number of processes occur at those times.
- C . The RAM on each VM is insufficient.
- D . The storage is overutilized.
A cross-site request forgery vulnerability exploited a web application that was hosted in a public laaS network. A security engineer determined that deploying a WAF in blocking mode at a CDN would prevent the application from being exploited again. However, a week after implementing the WAF, the application was exploited again.
Which of the following should the security engineer do to make the WAF control effective?
- A . Configure the DDoS protection on the CDN.
- B . Install endpoint protection software on the VMs
- C . Add an ACL to the VM subnet.
- D . Deploy an IDS on the laaS network.
A company just learned that the data in its object storage was accessed by an unauthorized party.
Which of the following should the company have done to make the data unusable?
- A . The company should have switched from object storage to file storage.
- B . The company should have hashed the data.
- C . The company should have changed the file access permissions.
- D . The company should have encrypted the data at rest.
A cloud engineer was deploying the company’s payment processing application, but it failed with the following error log:
ERFOR: root: Transaction failed http 429 response, please try again
Which of the following are the most likely causes for this error? (Select two).
- A . API throttling
- B . API gateway outage
- C . Web server outage
- D . Oversubscription
- E . Unauthorized access
- F . Insufficient quota
Which of the following provides secure, private communication between cloud environments without provisioning additional hardware or appliances?
- A . VPN
- B . VPC peering
- C . BGP
- D . Transit gateway
