ISACA CRISC Übungsprüfungen
Zuletzt aktualisiert am 30.04.2026- Prüfungscode: CRISC
- Prüfungsname: Certified in Risk and Information Systems Control
- Zertifizierungsanbieter: ISACA
- Zuletzt aktualisiert am: 30.04.2026
Which of the following BEST confirms the existence and operating effectiveness of information systems controls?
- A . Self-assessment questionnaires completed by management
- B . Review of internal audit and third-party reports
- C . Management review and sign-off on system documentation
- D . First-hand direct observation of the controls in operation
Which of the following helps ensure compliance with a nonrepudiation policy requirement for electronic transactions?
- A . Digital signatures
- B . Encrypted passwords
- C . One-time passwords
- D . Digital certificates
Which of the following should be the PRIMARY focus of an IT risk awareness program?
- A . Ensure compliance with the organization’s internal policies
- B . Cultivate long-term behavioral change.
- C . Communicate IT risk policy to the participants.
- D . Demonstrate regulatory compliance.
Which of the following changes would be reflected in an organization’s risk profile after the failure of a critical patch implementation?
- A . Risk tolerance is decreased.
- B . Residual risk is increased.
- C . Inherent risk is increased.
- D . Risk appetite is decreased
What is the PRIMARY reason an organization should include background checks on roles with elevated access to production as part of its hiring process?
- A . Reduce internal threats
- B . Reduce exposure to vulnerabilities
- C . Eliminate risk associated with personnel
- D . Ensure new hires have the required skills
Which of the following is the BEST method to track asset inventory?
- A . Periodic asset review by management
- B . Asset registration form
- C . IT resource budgeting process
- D . Automated asset management software
A risk practitioner is developing a set of bottom-up IT risk scenarios.
The MOST important time to involve business stakeholders is when:
- A . updating the risk register
- B . documenting the risk scenarios.
- C . validating the risk scenarios
- D . identifying risk mitigation controls.
After a high-profile systems breach at an organization s key vendor, the vendor has implemented additional mitigating controls. The vendor has voluntarily shared the following set of assessments:
Which of the assessments provides the MOST reliable input to evaluate residual risk in the vendor’s control environment?
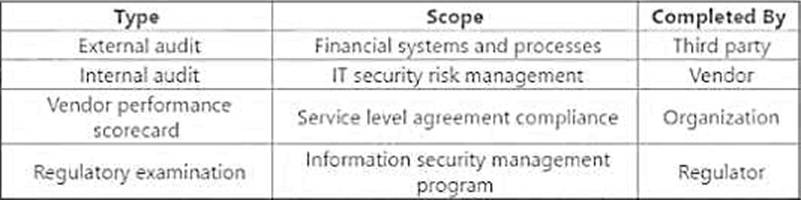
- A . External audit
- B . Internal audit
- C . Vendor performance scorecard
- D . Regulatory examination
Which of the following BEST supports ethical IT risk management practices?
- A . Robust organizational communication channels
- B . Mapping of key risk indicators (KRIs) to corporate strategy
- C . Capability maturity models integrated with risk management frameworks
- D . Rigorously enforced operational service level agreements (SLAs)
Which of the following is the MOST effective way to help ensure future risk levels do not exceed the organization’s risk appetite?
- A . Establishing a series of key risk indicators (KRIs)
- B . Adding risk triggers to entries in the risk register
- C . Implementing key performance indicators (KPIs)
- D . Developing contingency plans for key processes
